Fortinet FG-4401F-LENC HW FG-4401F-LENC
high Performance With Flexibilitythe Fortigate 4400f Series Enables Organizations To Build Security-driven Networks That Can Weave Security Deep Into Their Datacenter And Across Their Hybrid It Architecture To Protect Any Edge At Any Scale.powered By A Rich Set Of Ai/ml-based Fortiguard Services And An Integrated Security Fabric Platform, The Fortigate 4400f Series Delivers Coordinated, Automated, End-to-end Threat Protection Across All Use Cases.the Industry''s First Integrated Zero Trust Network Access (ztna) Enforcement Within An Ngfw Solution, Fortigate 4400f Automatically Controls, Verifies, And Facilitates User Access To Applications Delivering Consistent Convergence With A Seamless User Experience.fortios Everywhere | Fortios, Fortinet''s Advanced Operating Systemfortios Enables The Convergence Of High Performing Networking And Security Across The Fortinet Security Fabric. Because It Can Be Deployed Anywhere, It Delivers Consistent And Context-aware Security Posture Across Network, Endpoint, And Multi-cloud Environments.fortios Powers All Fortigate Deployments Whether A Physical Or Virtual Device, As A Container, Or As A Cloud Service. This Universal Deployment Model Enables The Consolidation Of Many Technologies And Use Cases Into A Simplified, Single Policy And Management Framework. Its Organically Built Best-of-breed Capabilities, Unified Operating System, And Ultra-scalability Allows Organizations To Protect All Edges, Simplify Operations, And Run Their Business Without Compromising Performance Or Protection.fortios Dramatically Expands The Fortinet Security Fabric''s Ability To Deliver Advanced Ai/ Ml-powered Services, Inline Advanced Sandbox Detection, Integrated Ztna Enforcement, And More, Provides Protection Across Hybrid Deployment Models For Hardware, Software, And Software-as-a-service With Sase.fortios Expands Visibility And Control, Ensures The Consistent Deployment And Enforcement Of Security Policies, And Enables Centralized Management Across Large-scale Networks With The Following Key Attributes: Interactive Drill-down And Topology Viewers That Display Real-time Status On-click Remediation That Provides Accurate And Quick Protection Against Threats And Abuses Unique Threat Score System Correlates Weighted Threats With Users To Prioritize Investigations Forticonverter Serviceforticonverter Service Provides Hassle-free Migration To Help Organizations Transition From A Wide Range Of Legacy Firewalls To Fortigate Next-generation Firewalls Quickly And Easily. The Service Eliminates Errors And Redundancy By Employing Best Practices With Advanced Methodologies And Automated Processes. Organizations Can Accelerate Their Network Protection With The Latest Fortios Technology.
Fortinet FSM-500G HW FSM-500G
unified Event Correlation And Risk Management For Modern Networksuptime Is A Mandate For Today''s Digital Business And End Users Do Not Care If Their Application Problems Are Performance Or Security-related. That''s Where Fortisiem Comes In.unified Noc And Soc Analytics (patented)fortinet Has Developed An Architecture That Enables Unified Data Collection And Analytics From Diverse Information Sources Including Logs, Performance Metrics, Snmp Traps, Security Alerts, And Configuration Changes. Fortisiem Essentially Takes The Analytics Traditionally Monitored In Separate Silos - Soc And Noc - And Brings That Data Together For A Comprehensive View Of The Security And Availability Of The Business. Every Piece Of Information Is Converted Into An Event Which Is First Parsed And Then Fed Into An Event-based Analytics Engine For Monitoring Real-time Searches, Rules, Dashboards, And Ad-hoc Queries.highlights | Machine Learning / Uebafortisiem Uses Machine Learning To Detect Unusual User And Entity Behavior (ueba) Without Requiring The Administrator To Write Complex Rules. Fortisiem Helps Identify Insider And Incoming Threats That Would Pass Traditional Defenses. High Fidelity Alerts Help Prioritize Which Threats Need Immediate Attention.user And Device Risk Scoringfortisiem Build A Risk Scores Of Users And Devices That Can Augment Ueba Rules And Other Analysis. Risk Scores Are Calculated By Combining Several Datapoints Regarding The User And Device. The User And Device Risk Scores Are Displayed In A Unified Entity Risk Dashboard.distributed Real-time Event Correlation (patented)distributed Event Correlation Is A Difficult Problem, As Multiple Nodes Have To Share Their Partial States In Real Time To Trigger A Rule. While Many Siem Vendors Have Distributed Data Collection And Distributed Search Capabilities, Fortinet Is The Only Vendor With A Distributed Real-time Event Correlation Engine. Complex Event Patterns Can Be Detected In Real Time. This Patented Algorithm Enables Fortisiem To Handle A Large Number Of Rules In Real Time At High Event Rates For Accelerated Detection Timeframes.real-time, Automated Infrastructure Discovery And Application Discovery Engine (cmdb)rapid Problem Resolution Requires Infrastructure Context. Most Log Analysis And Siem Vendors Require Administrators To Provide The Context Manually, Which Quickly Becomes Stale, And Is Highly Prone To Human Error. Fortinet Has Developed An Intelligent Infrastructure And Application Discovery Engine That Is Able To Discover Both Physical And Virtual Infrastructure, On-premises And In Public/ Private Clouds, Simply Using Credentials Without Any Prior Knowledge Of What The Devices Or Applications Are.an Up-to-date Cmdb (centralized Management Database) Enables Sophisticated Context Aware Event Analytics Using Cmdb Objects In Search Conditions.dynamic User Identity Mappingcrucial Context For Log Analysis Is Connecting Network Identity (ip Address, Mac Address) To User Identity (log Name, Full Name, Organization Role). This Information Is Constantly Changing As Users Obtain New Addresses Via Dhcp Or Vpn.fortinet Has Developed A Dynamic User Identity Mapping Methodology. Users And Their Roles Are Discovered From On-premises Or Cloud Sso Repositories. Network Identity Is Identified From Important Network Events. Then Geo-identity Is Added To Form A Dynamic User Identity Audit Trail. This Method Makes It Possible To Create Policies Or Perform Investigations Based On User Identity Instead Of Ip Addresses - Allowing For Rapid Problem Resolution.
Fortinet FAD-4200F-DC FORTIADC-4200F-DC APPLICATION DELIVERY CONTROLLER - 4 X 40GBE QSFP+, 8 X 10GBE S
application Delivery With Security And Optimization In Recent Years, The Landscape Of Application Delivery Has Undergone Significant Transformations Influenced By Evolving Technology Trends And The Increasing Adoption Of Cloud Computing. Many Organizations Are Integrating On-premises Data Centers With Public Cloud Environments To Optimize Application Performance, Enhance Scalability, And Improve Overall Business Agility.introductionfortiadc, The Advanced Application Delivery Controller (adc), Optimizes Application Delivery, Enhances Performance, And Ensures Application Security Whether Hosted On-premises Or In The Cloud.fortiadc Offers Robust L4-l7 Load-balancing Capabilities With Scripting Support For Content Manipulation And Advanced Ssl Services (offloading And Mirroring).fortiadc Also Offers Application Acceleration, Authentication, And Built-in Security Features Like Web Application Firewall Protection For Any Application Threats (owasp-top10 Compliance), Ddos Protection, Ztna, And More.with Flexible Deployment Options (hw, Vm, Fortiflex, And Cloud Providers) And Integration Into The Fortinet Security Fabric, Fortiadc Empowers Businesses To Deliver Exceptional Application Experiences And Security.highlights | Application Availability Applications Are The Lifeblood Of A Company''s Online Presence. Unresponsive Applications Can Result In Lost Revenue And Customers Taking Their Future Business Elsewhere. Application Performance, Scalability, And Resilience Are Key But None Of This Matters Unless The End-user Has A Good Experience And Completes Their Transaction.fortiadc Is A Dedicated Application Delivery Control Solution That Provides A Multi-tenancy Solution (vdom And Adom), High Availability, And Scalability With Hybrid Solution Deployment (on-premises And Cloud Offering) To Your Applications.web Application Protection Fortiadc Offers Multiple Levels Of Protection To Defend Against Attacks That Target Your Web Applications. Fortiadc Web Application Firewall Provides Multi Layer Protection Against The Owasp Top 10 Application Attacks Including Web Signatures To Defend Against Known And Unknown Attacks Along With Apis Security To Protect Against Malicious Actors By Automatically Enforcing Security Policies. Seamlessly Integrate Api Security Into Your Ci/cd Pipeline.application Anywhere (gslb) Fortiadc''s Included Global Server Load Balancing (gslb) Module On-prem Or In The Cloud (fortigslb Cloud) Makes Your Network Reliable And Available By Scaling Applications Across Multiple Data Centers For Disaster Recovery Or To Improve Application Response Times. Customers Can Set Up Rules Based On Site Availability, Data Center Performance, And Network Latency.highlights Continued | Data Optimizationfortiadc Provides Multiple Services That Speed The Delivery Of Applications To Users. The Pagespeed Suite Of Website Performance Enhancement Tools Can Automatically Optimize Http, Css, Javascript, And Image Delivery To Application Users. Fortiadc Also Provides Dynamic Caching And Http Compression And Decompression To Improve End-user Experience And Server Productivity.application Access Management Fortiadc Provides Centralized User Authentication And Authorization Services To Web Applications. Fortiadc Acts As A Gatekeeper To Offload Http Authentication And Authorization To Customer Applications Using Single Sign-on (sso) Services, Saml, Ldap, Radius, And Mfa (using Fortitoken Cloud And Google Authenticator).
Fortinet FG-40F-BDL-809-12 40F - security appliance - with 1 year FortiCare Premium Support
Fortinet FortiGate 40F - security appliance - with 1 year FortiCare Premium Support + 1 year FortiGuard Enterprise
Fortinet FG-40F-BDL-809-36 40F HARDWARE PLUS 3 YEAR HARDWARE PLUS FORTICARE
FORTIGATE-40F HARDWARE PLUS 3 YEAR HARDWARE PLUS FORTICARE FG-40F-BDL-809-36 Fortinet, Inc FG-40F-BDL-809-36 Fortinet, Inc
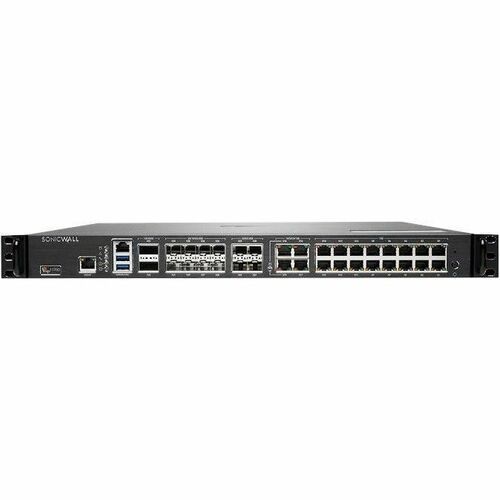
SonicWall 02-SSC-2293 SONICWALL NSSP 11700 SECURE UPGRADE APPLIANCE ONLY NO ATTACHED SUBSCRIPTION (EX
the Sonicwall Network Security Services Platform™ (nssp) Series Has Next-generation Firewalls With High Port Density And Multi-gig Speed Interfaces, That Can Process Several Million Connections For Zero-day And Advanced Threats. Designed For Large Enterprise, Higher Education, Government Agencies And Mssps, It Eliminates Attacks In Real Time Without Slowing Performance. It Is Designed To Be Highly Reliable And Deliver Uninterrupted Services To Organizations.enterprise-class Firewallsas Businesses Evolve Along With An Increase In Managed And Unmanaged Devices, Networks, Cloud Workloads, Saas Applications, Users, Internet Speeds, And Encrypted Connections, A Firewall That Can''t Support Any One Of These Becomes A Bottleneck. A Firewall Should Be A Source Of Strength And Not A Point Of Weakness.the Sonicwall Nssp Firewall''s Multiple 100g/40g/25g/10g Interfaces Allow You To Process Several Million Simultaneous Encrypted And Unencrypted Connections With Unparallel Threat Prevention Technology. With More Than 70% Of All Sessions Being Encrypted, Having A Firewall That Can Process And Examine This Traffic Without Impacting The End User Experience Is Critical To Productivity And Information Security.the Nssp 15700''s Unified Policy Enables Organizations To Simply And Intuitively Create Access And Security Policies In A Single Interface.simplified Management And reporting Ongoing Management, Monitoring And Reporting Of Network Activities Are Handled Through The Sonicwall Network Security Manager. This Provides An Intuitive Dashboard For Managing Firewall Operations As Well As Provide Historical Reports - From A Single Source. Together, The Simplified Deployment And Setup Along With The Ease Of Management Enable Organizations To Lower Their Total Cost Of Ownership And Realize A High Return On investment.deployment | Next-generation Firewall (ngfw) Managed Through A Single Pane Of Glass Nssp Integrates With The Rest Of The Sonicwall Ecosystem Of Solutions Gain Full Visibility Into Your Network To See What Applications, Devices, And Users Are Doing To Enforce Policies As Well As Eliminate Threats And Bandwidth Bottlenecks Integrate With Capture Atp With Rtdmi For Cloud-based Sandboxing Or Capture Security Appliance For On-premise Malware Detectiondeep Packet Inspection Of Ssl/ Tls (dpi-ssl) For Hidden Threats The Nssp Provides Inspection For Over Millions Of Simultaneous Tls/ssl And Ssh Encrypted Connections Regardless Of Port Or Protocol Inclusion And Exclusion Rules Allow Customization Based On Specific Organizational Compliance And/or Legal Requirements Support For Tls Cipher Suites Up To Tls 1.3
SonicWall 02-SSC-2291 SONICWALL NSSP 10700 SECURE UPGRADE APPLIANCE ONLY NO ATTACHED SUBSCRIPTION (EX
the Sonicwall Network Security Services Platform™ (nssp) Series Has Next-generation Firewalls With High Port Density And Multi-gig Speed Interfaces, That Can Process Several Million Connections For Zero-day And Advanced Threats. Designed For Large Enterprise, Higher Education, Government Agencies And Mssps, It Eliminates Attacks In Real Time Without Slowing Performance. It Is Designed To Be Highly Reliable And Deliver Uninterrupted Services To Organizations.enterprise-class Firewallsas Businesses Evolve Along With An Increase In Managed And Unmanaged Devices, Networks, Cloud Workloads, Saas Applications, Users, Internet Speeds, And Encrypted Connections, A Firewall That Can''t Support Any One Of These Becomes A Bottleneck. A Firewall Should Be A Source Of Strength And Not A Point Of Weakness.the Sonicwall Nssp Firewall''s Multiple 100g/40g/25g/10g Interfaces Allow You To Process Several Million Simultaneous Encrypted And Unencrypted Connections With Unparallel Threat Prevention Technology. With More Than 70% Of All Sessions Being Encrypted, Having A Firewall That Can Process And Examine This Traffic Without Impacting The End User Experience Is Critical To Productivity And Information Security.the Nssp 15700''s Unified Policy Enables Organizations To Simply And Intuitively Create Access And Security Policies In A Single Interface.simplified Management And reporting Ongoing Management, Monitoring And Reporting Of Network Activities Are Handled Through The Sonicwall Network Security Manager. This Provides An Intuitive Dashboard For Managing Firewall Operations As Well As Provide Historical Reports - From A Single Source. Together, The Simplified Deployment And Setup Along With The Ease Of Management Enable Organizations To Lower Their Total Cost Of Ownership And Realize A High Return On investment.deployment | Next-generation Firewall (ngfw) Managed Through A Single Pane Of Glass Nssp Integrates With The Rest Of The Sonicwall Ecosystem Of Solutions Gain Full Visibility Into Your Network To See What Applications, Devices, And Users Are Doing To Enforce Policies As Well As Eliminate Threats And Bandwidth Bottlenecks Integrate With Capture Atp With Rtdmi For Cloud-based Sandboxing Or Capture Security Appliance For On-premise Malware Detectiondeep Packet Inspection Of Ssl/ Tls (dpi-ssl) For Hidden Threats The Nssp Provides Inspection For Over Millions Of Simultaneous Tls/ssl And Ssh Encrypted Connections Regardless Of Port Or Protocol Inclusion And Exclusion Rules Allow Customization Based On Specific Organizational Compliance And/or Legal Requirements Support For Tls Cipher Suites Up To Tls 1.3
Digi X4-Z11-E-W CONNECTPORT X4 XBEE ETH RS-232 SEC INTL
remote M2m Device Networking Gateways Designed For Commercial Grade And Rugged Outdoor Applicationsconnectport X4 Customizable 3g Cellular M2m Routing Gateways Offer A Variety Of Lan/wan Interface Options For Endto-end Networking Of Remote Devices. The Gateways Include Comprehensive Ip Protocols And Ipsec Vpn Support For Highend Routing And Security. The Easy Dia/python Development Environment Enables Custom Applications To Run Locally While Interfacing Across Cellular Networks For Wan Connectivity To A Centralized Server.connectport X4 Gateways Feature A Compact Commercial Grade Enclosure Or An Optional Outdoors Ip66/nema 4x Enclosure With Class 1, Division 2 Rating For More Rugged Applications.
Get a Quote
Item(s) added to cart
Netgear GS105E-200NAS ProSafe Plus Switch, 5-Port Gigabit Ethernet - 5 Ports - 2 Layer Supported - Wall Mountable - Lifetime Limited Warranty-None Listed Compliance
MFR: Netgear, Inc
Qty: 1
Part #: GS105NA